Before a faulty software update dragged the company’s name into global headlines on Friday, Crowdstrike had a long history of involvement with US intelligence agencies, and played a key role in the ‘Russiagate’ hoax.
Crowdstrike released a defective update to its cloud-based security software on Friday that left an array of users around the world – including banks, airlines, media outlets, and government agencies – unable to use their IT systems.
The company issued a fix within several hours of the problem being identified, but thousands of flights remained canceled or delayed into Friday afternoon, while hospitals, police departments, and businesses continued to report issues getting back online.
[...]
Less than a year after Crowdstrike was founded, Kurtz and Alperovitch brought on board former FBI Executive Assistant Director Shawn Henry to head up its cybersecurity consultation wing. By 2014, Henry’s department was issuing a flurry of hacking and espionage accusations against China, Russia, and North Korea, with information provided by Crowdstrike helping the US Justice Department issue indictments that summer against five Chinese military officers who allegedly hacked US energy corporations.
[...]
Crowdstrike was hired by the US Democratic National Committee to investigate the theft of data from its servers in 2016. Published by WikiLeaks, the data revealed that the DNC had rigged the Democratic primary against Bernie Sanders, and that Hillary Clinton had effectively paid to control the committee.
Crowdstrike concluded that Russia was behind the breach, with Henry testifying to Congress that the company “saw activity that we believed was consistent with activity we’d seen previously and had associated with the Russian government.”
I remember testing their software many years ago and asking myself, what the fuck does it actually do? There was no control. How do I scan and remove threats? It was just a fancy dashboard with bullshit metrics
Point 8.6
Its also a funny thing. I mean, somehow thought: "its okay. They say not to use it in places where fault tolerance is important, but let's do it anyway".
That was what I noticed too, and we just evaluated it and I couldn't see the utility in any of their stupid graphs. Why to I need to see this graph of the malware "moving laterally" when this graph is post facto... I'll already be infected with something. I don't need yet another way to run remote commands on my end points, I can just do it with powershell.
I don't call the shots ultimately, so whatever, but I was not impressed. Just age old signatures with paint and plaster covering it.
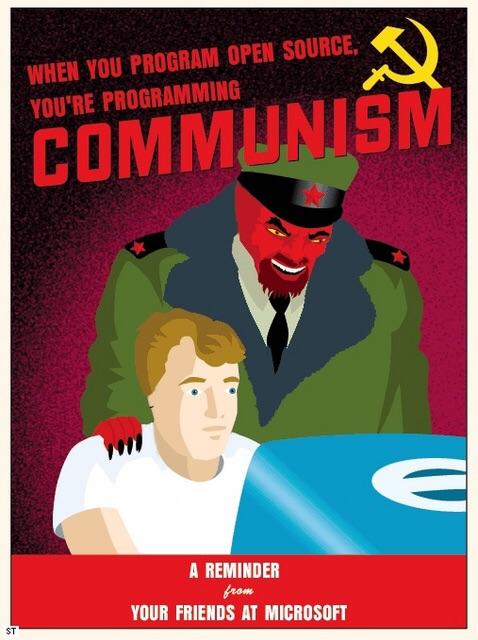
Honestly, Death to Microsoft.