I have a few Linux servers at home that I regularly remote into in order to manage, usually logged into KDE Plasma as root. Usually they just have several command line windows and a file manager open (I personally just find it more convenient to use the command line from a remote desktop instead of directly SSH-ing into the system), but if I have an issue, I've just been absentmindedly searching stuff up and trying to find solutions using the preinstalled Firefox instance from within the remote desktop itself, which would also be running as root.
I never even thought to install uBlock Origin on it or anything, but the servers are all configured to use a PiHole instance which blocks the vast majority of ads. However, I do also remember using the browser in my main server to figure out how to set up the PiHole instance in the first place, and that server also happens to be the most important one and is my main NAS.
I never went on any particularly shady websites, but I also don't remember exactly which websites I've been on as root, though I do seem to remember seeing ads during the initial pihole setup, because it didn't go very smoothly and I was searching up error messages trying to get it to work.
This is definitely on me, but it never crossed my mind until recently that it might be a bad idea to use a browser as root, and searching online everyone just states the general cybersecurity doctrine to never do it (which I'm now realizing I shouldn't have) but no one seems to be discussing how risky it actually is. Shouldn't Firefox be sandboxing every website and not allowing anything to access the base system? Between "just stop doing it" and "you have to reinstall the OS right now there's probably already a virus on there," how much danger do you suppose I'm in? I'm mainly worried about the security/privacy of my personal data I have stored on the servers. All my servers run Fedora KDE Spin and have Intel processors if that makes a difference?
You seriously need to stop what you're doing. Log in with ssh only. If you need multiple terminals use multiple ssh sessions, or screen/tmux. If you need to search something do it on your desktop system.
The server should not have Firefox installed, or KDE, or anything related to desktop apps. There's no point and nothing good can come of it.
Realistically it's not super dangerous, and no you probably don't have a virus just from browsing a few tech support sites, but you do eliminate your last line of defense when you run software as root. As you know, root can read/change/delete anything on your system whereas regular users are generally restricted to their own data. So if there is a security problem in the software, it's made worse by the fact that you were running it as root.
You are right though that Firefox does still have its own protections - it's probably one of the most hardened pieces of software on your computer exactly because it connects to the whole wide internet - and those protections are not negated by running as root. However if those protections fail, the attacker has the keys to the kingdom rather than just a sizable chunk of the kingdom.
To put that in perspective though, if there is a Firefox exploit and a hacker gets access to your regular user account, that's already pretty bad in itself. Even if you run as a regular unprivileged user they would still have have access to things like: your personal documents, your ssh keys, your Firefox profile with your browsing history, your session cookies and your saved passwords, your e-mail, your paypal account, your banking information, ...
As root, they could obviously do even more like damage like reading all users' data, installing a keylogger or screengrabber, installing a rootkit to make themselves undetectable, but for most regular users most of the damage is already done when their own account is compromised.
So when these discussions come up, I always have to think about this XKCD comic:
Show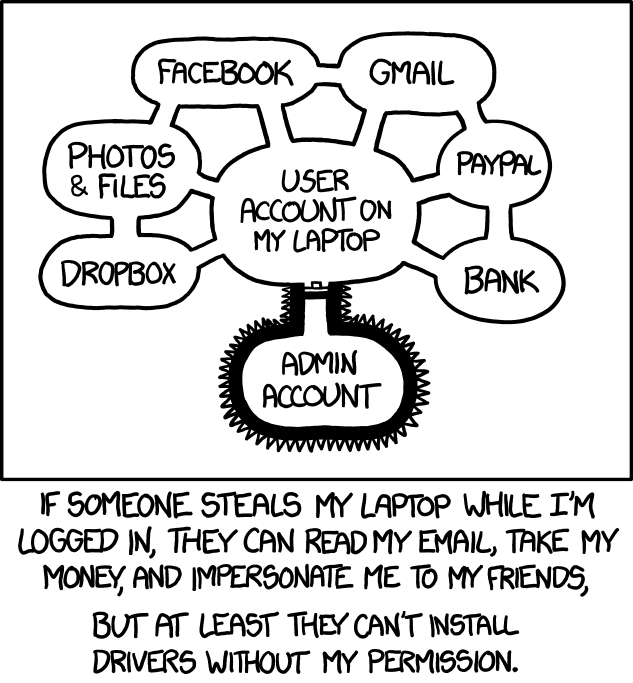
It's about as dangerous as using IE in the old days, or Edge in administrator mode.
Just don't do that 😁
I don't get it anyway, if you login remotely, why don't you just open firefox locally but on the remote servers? This makes not much sense.
But If you absolutely have to. .. At least be careful with your surf-targets. A search-engine and wiki would most likely be fine. Some pron-, stream- or warez-sites? Nah. Surely not.
Yes, it is. As a user you compromise only that user as a consequence of some sandbox escape. Then there may or may not be some successful privilege elevation.
Without any judgement: why are your servers running X11? Just because you dislike SSH'ing to them?
Mainly that. I want to be able to have multiple terminal windows open and have them stay open independent of my main PC. Part of the reason I have a file server instead of plugging all the drives into my PC is so I can offload processor heavy operations onto it (namely making archives and compressing files for long term storage) so I don't have to use my PC for that.
People have mentioned programs like screen but IMO it's way more annoying to juggle multiple terminals with it than if they were just windows, and also screen doesn't scroll so whatever goes beyond the top edge is just inaccessible which I find really annoying. I've also been screwed by mistyped file operations on the terminal before (deleting stuff I didn't mean to mainly) and I just find it safer to use a GUI file manager where it's a lot harder to subtly mess something up and not notice until it's too late.
screen doesn’t scroll
Screen (and any other muxer) can scroll just fine. You just have to learn how to do it in each one. Tmux, for example, is
ctrl+b [to enter scroll mode.mistyped file operations
Get a good TUI file manager. I use and recommend ranger.
Screen uses Ctrl-a Esc (you press Ctrl+a, release them and then tap Esc, then you can scroll with arrows or pup/pgdown)
tmux has long been the better replacement to screen. SFTP makes it so you can use desktop software for file system operations.
Hmm, I see. The perfectionist in me would want to shed that processor load though ^^
Usig anything as root is a security risk.
Using any UI application as root is a bigger risk. That's because every UI toolkit loads plugins and what not from all over the place and runs the code from those plugins (e.g. plugins installed system wide and into random places some environment variables point to). Binary plugins get executed in the context of the application running and can do change every aspect of your program. I wrote a small image plugin to debug an issue once that looked at all widgets in the UI and wrote all the contents of all text fields (even those obfuscated to show only dots in the UI) to disk whenever some image was loads. Plugins in JS or other non-native code are more limited, but UI toolkits tend to have binary plugins.
So if somebody manages to set the some env vars and gets root to run some UI application with those set (e.g. using sudo), then that attacker hit the jackpot. In fact some toolkits will not even bring up any UI when run as root to avoid this.
Running any networked UI application as root is the biggest risk. Those process untrusted data by definition with who knows what set of plugins loaded.
Ideally you run the UI as a normal user and then use sudo to run individual commands as root.
So is the main worry with GUIs that they have potential code execution vulnerabilities? Or is the worry that the plugins themselves are malicious?
Plugins are a code execution vulnerability by design;-) Especially with binary plugins you can call/access/inspect everything the program itself can. All UI toolkits make heavy use of plugins, so you can not avoid those with almost all UI applications.
There are non-UI applications with similar problems though.
Running anything with network access as root is an extra risk that effects UI and non-UI applications in the same way.
On a typical home user desktop linux setup, there's virtually no difference between your regular user and root.
Access to your data, emails, passwords, installing software (in /home), access to LAN and so on are already possible without root permissions, so there really is not a whole lot that an attacker cannot do even without root.
And then, if you use sudo or su (or whatever) to switch to root with a password, escalating to root privileges is basically trivial for an attacker. An attacker can divert your PATH to compromised binaries. They could just replace "sudo" with their own little script that steals your password.
Firefox does sandbox everything but vulnerabilities exist and sometimes go unnoticed for a while before they're discovered and patched. If a malicious script does manage to escape the sandbox it will be able to do literally anything to the system since it has root privileges. It would have full access to any device that's in /dev, it could create, modify and delete udev or iptables rules, it could mess with the BIOS since the kernel exposes EFI variables, if the mainboard has re-writable flash chips for the firmware it could write malicious code to them since they may show up in /dev, etc. If any of this makes you uneasy then you probably should stop running stuff as root in general except for when you really need to.
Also in general you don't want to run any graphical applications on a Server unless there is a very specific reason for it because it takes up extra resources and therefore makes the machine use more power overall. This is especially bad when the machine in question has no hardware acceleration and renders everything in software. Remote desktop also adds CPU/GPU load and takes up a good bit of I/O and network bandwidth which is not ideal for a NAS server.





