Why do so many companies and people say that your password has to be so long and complicated, just to have restrictions?
I am in the process of changing some passwords (I have peen pwnd and it’s the password I use for use-less-er sites) and suddenly they say “password may contain a maximum of 15 characters“… I mean, 15 is long but it’s nothing for a password manager.
And then there’s the problem with special characters like äàáâæãåā ñ ī o ė ß ÿ ç just to name a few, or some even won’t let you type a [space] in them. Why is that? Is it bad programming? Or just a symptom of copy-pasta?
Yes its bad programing. These restrictions suggest that the company is either doing improper storage and processing, or does not understand how to deal with passwords.
The proper password storage is a hash. This is a cryptographic function that is easy to do and imbossible to undo. The hash function operates on the underlying binary representation of your password, and doesn't card what letters or symbols are in it. A program should take your password, hash it, and compare the result to the hash they have in their detebase.
The current recomended hash algorythm is called 'bcrypt'. Depending on the implementation, the input is between 50 and 70 bytes (the spec was a little unclear so people defined the inputs diferently, but the algorithe is the same). This means a password should be able to take at least 50 normal keyboard characters, including letters, symbols, and spaces. Anything less than that indicates a poor practice on behalf of the website.
(a lot of this is simplified. There is some variation and nuance that I don't think affects the main idea)
Every time I find a site like this, I assume the programming is bad and the security is poor. (They don't know how to sanitize input? They don't know how to hash passwords?) It's a good reason to use random passwords on every site for when that one is compromised.
What is "funny" is that I had the maximum password size thing on several bank websites (and a low one, at that). Fortunately, with 2FA, it doesn't really matter I guess.
The new NIST guidance is to have something long. Special characters don't matter. So a good passphrase that you can remember > short line noise. NIST also recommends against constant password rotation, but to instead audit for dictionary attacks. See also: https://www.netsec.news/summary-of-the-nist-password-recommendations-for-2021/
Yes, it is bad programming. Of course, on the backend you must never store passwords in the clear. You should never grow your own hashing algorithm.
Non-ASCII characters can cause troubles because of different encodings and because you may need to type them on a machine where corresponding keyboard layout is missing.
The password length limit is nothing short of stupid.
Show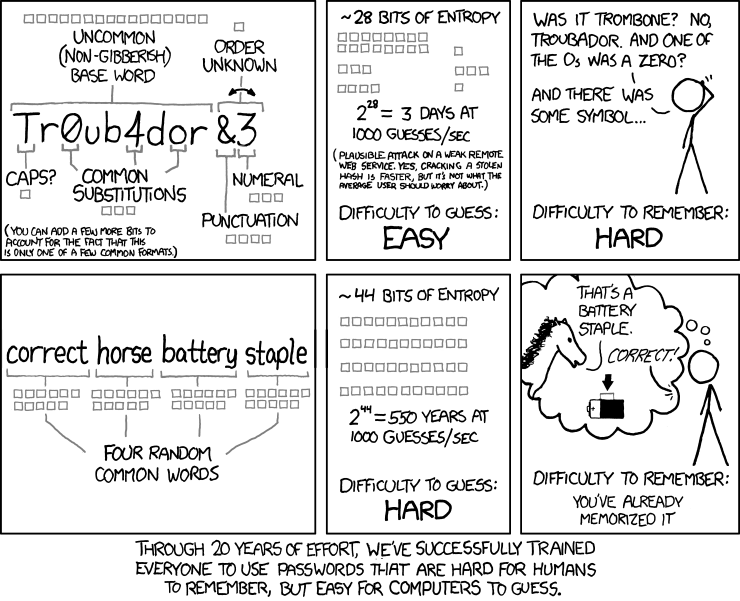
My mother’s password for everything got compromised recently. I told her to think of a sentence that will never happen and to write it down and store it somewhere safe.
She remembered it instantly.
Oh, and I made her a password manager
Likely more bad design than bad programming, but that's not a very meaningful distinction.
It's downright scary how many "professionals" are onboard with this shit.
Some of the restrictions are there to try and protect users from themselves. Most people don't want to put a space in their password so it's assumed it was a mistake when they do.
Just my general experience, I mean how many passwords from leaked password lists contain spaces? The general understanding of passwords is that they contain no spaces
I mean how many passwords from leaked password lists contain spaces?
Eh... There are no passwords with spaces in the leaks, because hardly any service allows it? After all, that's what this whole thread is about.
I'm sure it's a chicken and egg situation then, a few services do allow it but I've never come across someone using it intentionally outside of people doing it specifically because it's uncommon