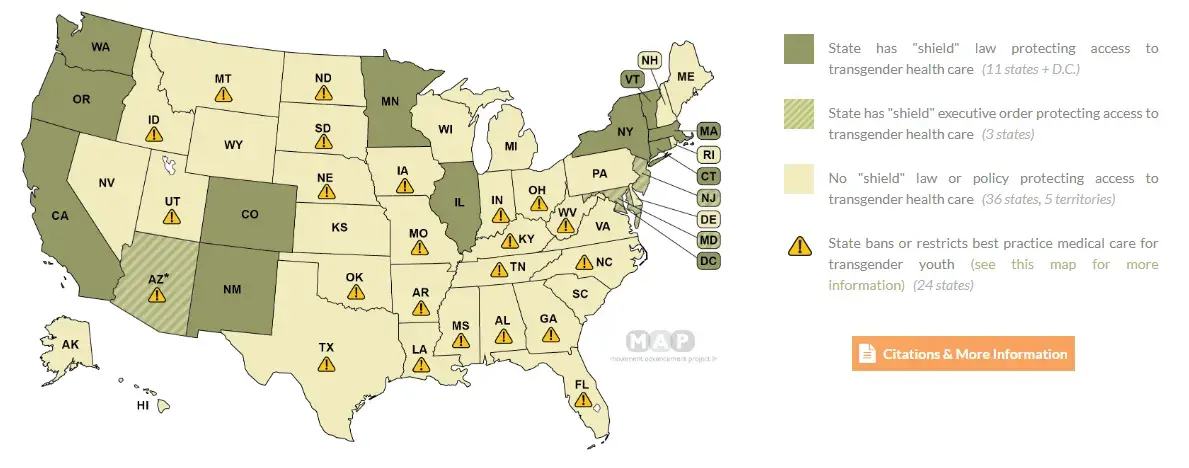
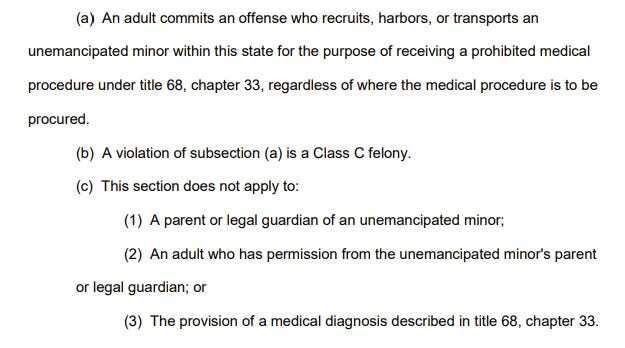
Tennessee has recently passed a bill, effective July 1st 2024, declaring it a class-C felony to "recruit, harbor, or transport an unemancipated minor within this state" for transgender healthcare procedures, carrying a sentence of 3-15 years in prison. This applies over state lines and states that do not have anti-extradition laws relating to trans rights can extradite you to Tennessee.
Notably: the bill is vague. This means: telling stories of your own transition, describing your healthcare experiences to an open group chat, describing your trans experiences on a public website, creating trans health guides online, describing how you have gotten DIY HRT, describing anything to do with trans healthcare, even as a cis person, can result in a class-C felony conviction.
Given that being arrested in any capacity for transgender people can be an incredibly dangerous experience (CW: SV), I strongly suggest you begin caring about opsec, stop referring to where you live, use VPNs, stop using apps like Discord, and stop using social media sites that track your IP or user agent fingerprint while unprotected. Remember that for a bill like this to be challenged in court, you have to be arrested first.
Will discuss creating / linking to a transgender matrix chat so that we can help people to move off of things like discord.


I wouldn't knock it until I learn of a situation where Signal handed data over to the government that wasn't encrypted mishmash or derived from side-channel that wasn't specifically related to Signal (the app or the protocol) itself. I do fully agree, however, that a phone number as a registration ID is bad.
But as it stands I don't consider the point that it's located in the USA to be fully incriminating. Just as I don't find it a problem that Matrix and Vector Creations were an offshoot from an Israeli tech company*. The protocol, and how it functions, are what matters.
*And yes, the major caveat here is that you can inspect and run the Matrix server code (Synapse or Dendrite), but not the Signal server code.
Read the section on NSL's (national security letters) in the link above. Any US domiciled company must give up it's data when asked, and it's illegal for them to tell their users they were forced to do so. The Obama regime admitted to issuing 60 of these every single day, there's no way Signal isn't compromised.
Matrix doesn't need to be hosted in the US, so they don't have that problem. Using any US-hosted service is a big no-no.
This is neither new information, nor something overlooked in the design of the software. Thats the point of end to end encryption and open source code: they can only give the data that they have access to, which is the sender, receiver, and timestamps, but we know they cannot decrypt messages in the middle, because it would show in the security implementation in the source code. This model prevents the carrier from knowing the contents of any messages they carry. Therefore, you have to attack one of the end point devices to get the contents, and all the warrants and secret letters in the world can't compell then to give up the content of your messages, because they do not have the means to do so.
There are legitimate problems with the security model, like its use of phone numbers as account identifiers, that render it a poor choice for doing Certain Things, but that alone does not prove it was designed as a honeypot, or that it has been secretly compromised in some way that can't be seen in the source code.
This really is worth emphasizing, because there are cases where we can reason about the kinds of exploits and vulnerabilities that do happen based on what we learn after the fact, or based on things that companies say they do or must do by implication even if they don't outright say it.
For example, I do not recommend Apple's iMessage. Why? It's an encrypted chat service, after all.
It's because when you use iCloud Backup they store the private keys. If they hold the private keys, they can decrypt the encrypted data whenever they're subpoenaed or whatever else. So if either party (you or your recipient) has this common feature enabled, your entire chat history is up for grabs. Apple themselves basically say as much here https://support.apple.com/en-gb/guide/security/sec3cac31735/web
Bonus reading. https://www.reuters.com/article/us-apple-fbi-icloud-exclusive/exclusive-apple-dropped-plan-for-encrypting-backups-after-fbi-complained-sources-idUSKBN1ZK1CT/