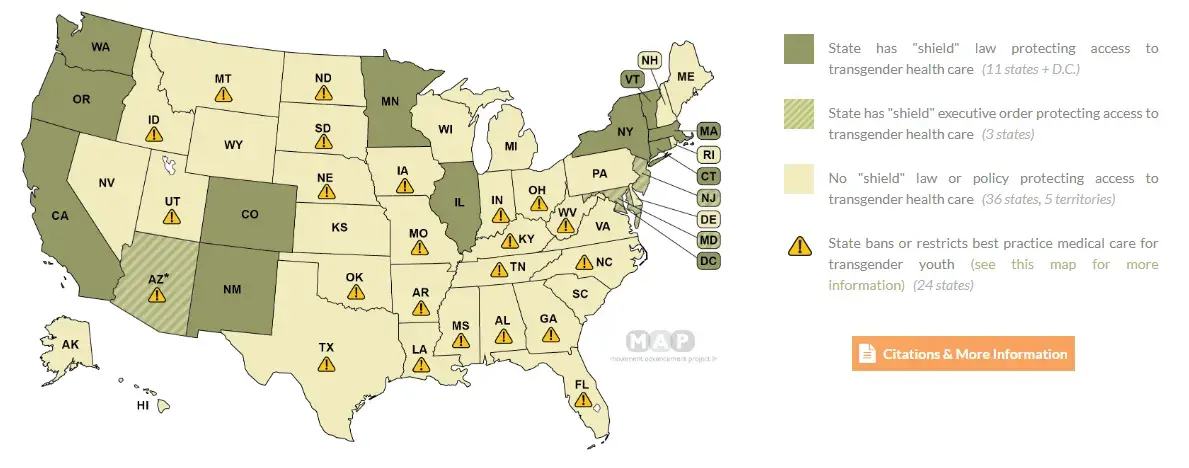
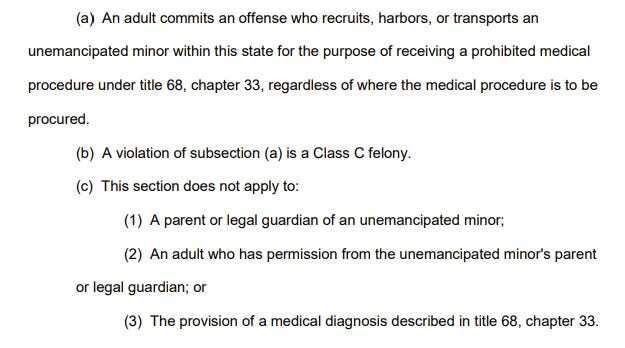
Tennessee has recently passed a bill, effective July 1st 2024, declaring it a class-C felony to "recruit, harbor, or transport an unemancipated minor within this state" for transgender healthcare procedures, carrying a sentence of 3-15 years in prison. This applies over state lines and states that do not have anti-extradition laws relating to trans rights can extradite you to Tennessee.
Notably: the bill is vague. This means: telling stories of your own transition, describing your healthcare experiences to an open group chat, describing your trans experiences on a public website, creating trans health guides online, describing how you have gotten DIY HRT, describing anything to do with trans healthcare, even as a cis person, can result in a class-C felony conviction.
Given that being arrested in any capacity for transgender people can be an incredibly dangerous experience (CW: SV), I strongly suggest you begin caring about opsec, stop referring to where you live, use VPNs, stop using apps like Discord, and stop using social media sites that track your IP or user agent fingerprint while unprotected. Remember that for a bill like this to be challenged in court, you have to be arrested first.
Will discuss creating / linking to a transgender matrix chat so that we can help people to move off of things like discord.


Didn’t Signal recently get outed as having a back door?
Honestly, as long as you're using a phone, you're at risk. As LLMs becomes more portable it's just a matter of time before our own phones will narc on us. Most of them already have some sort of ocr /image describer process happening on our photo rolls.
I think that’s where threat modeling comes in. Unfortunately, if you’re threat modeling against the US government, you’re mostly relying on the laziness and ineptitude of some random LEO to not follow through on looking into you further. You can absolutely make things better, but if you get a target on your back you’re fucked. There’s a reason Snowden’s in Russia.
Personally, I think we need some of our more electronically inclined comrades to start thinking about putting the punk in our cyber dystopia. Microcontrollers like the ESP32 are cheap and capable enough that we could be building devices that are less complicated and more singularly focused on getting people connected to tor based sites or something along those lines.
people are trying. Well idk about tor specifically but a decent number of people are working on linux phones, or simpler open source devices along those lines. Problem with a torphone or whatever is at some point you need to connect, whether it's to wifi, 4G, etc. and that's where you're going to see bottlenecks, surveillance, attempts at blocking tor, etc. Plus most people don't want to be that secure, they want to be able to use normal apps, calling, texting, etc.
Honestly a wifi-only tor messenger would be interesting but I'd have to do some research to see what sufficiently paranoid messaging stack exists and whether it can run on low power devices.
Wifi is plentiful and often easily cracked.
https://youtu.be/1ibg0tgVugY
One of the first topics I cover whenever I'm in a new study group is wifi authentication handshakes and some of the many ways to capture them.
https://youtu.be/dZwbb42pdtg
Specifically, with a $6 esp32
https://github.com/risinek/esp32-wifi-penetration-tool -this is not ideal as it requires the esp32 disconnecting from the user in order to do the sniffing. But it's the perfect starting point. Much better would be a serial based menu or a Bluetooth app to control it, imo.
These authentication packets can then be cracked using hashcat and your basic gaming PC with GPU.
https://youtu.be/Usw0IlGbkC4 - disclaimer, I haven't watched this video. Just a random hashcat vid I'm sure there's something better out there.
My mindset is largely something like this:
I don't expect your average person to be out there flashing an esp32 or anything, but every group should have a tech person that can teach their people these basic concepts and provide them with hardware like an esp32 to do it with. Imo, we need like a basic set of best practices and tutorials that every group's tech person can draw from to support their people. Heck, we probably need a manual that covers something like that for each role. Turnkey leftist group manual, if you will.
I found YouTube links in your comment. Here are links to the same videos on alternative frontends that protect your privacy:
Link 1:
Link 2:
Link 3:
regular people aren't going to deal with multiple devices like that. smartphones are worse at every end-user function they provide than a dedicated device (except maybe cameras, although you wouldn't hold a regular ass camera the wrong way when taking pictures...) but they're decent enough and you only have to keep track of one thing.
shit i know better and i'd sooner replace a smartphone with nothing than carry around six different things to replace it.
Can you post a source? Because I haven't heard such a thing.
There have been rumors for years but as far as I know nobody has been able to substantiate the claim. The organization that eventually produced Signal, Open Whisper Networks, received some seed funding from the Broadcasting Board of Governors (today known as the US Agency for Global Media), from which has been spun some CIA fronts like Radio Free Asia. However, this is also true of Tor, and many other non-profit private communications projects during this time, and does not itself prove any technical subversion has taken place. The source code for both the server and client are open source, and have been subject to frequent scrutiny, including full independent audits and penetration testing. No backdoor has ever been shown to exist in the code itself. Beyond that, people mostly gesture towards Moxie Marlinspike's radlib posturing and bad hair and invite people to Draw Their Own Conclusions.
No.